Calling on Cybersecurity Innovators: Help Utilities Improve Authentication for Distributed Energy Systems
Utilities need cybersecurity solutions that are easy to implement and can make a real-world difference immediately. That is why the theme for the first cohort of the new Clean Energy Cybersecurity Accelerator (CECA) is strong authentication for distributed energy resources.
"This is an immediate area of concern and interest to our utility partners because these are challenges they are facing right now," said Jared Macon, group manager for Cybersecurity Evaluation and Application at the National Renewable Energy Laboratory (NREL).
CECA is a private-public partnership between NREL, the U.S. Department of Energy's (DOE's) Office of Cybersecurity, Energy Security, and Emergency Response (CESER), the DOE Office of Energy Efficiency and Renewable Energy (EERE), and major utilities from across the United States, including Berkshire Hathaway Energy and Duke Energy. The program aims to expedite the commercialization of innovative cybersecurity technologies that utilities can take advantage of early on to secure the energy grid.
The CECA organizers hope the list of utility partners continues to increase, no matter the size of the utility.
"It's a huge advantage in our goal to secure the grid to partner with the companies that are on the frontlines—this allows us to have a rapid, real-world, and substantial impact," Jon White, director of NREL's Cybersecurity Program Office, said. "All utilities are welcome, invited, and encouraged to join. The more partners we can reach, the sooner we can get these disruptive solutions in place. This first cohort gives us a chance to set an example of success."
Operational technology (OT) that underpins distributed energy resources (DERs) is lacking when it comes to enforcing authentication and authorization, as this type of distributed model was not part of the original system designs. The "strong" in strong authentication is a defined term used in security standards, and it means having more than one factor, or multifactor, to authenticate the user is the person they claim to be. In essence, it is something the user knows, such as a password, something the user has, such as a token, phone, or digital certificate, or something personal about the user, such as a fingerprint or palm reader, or an eye scan.
Authentication is often known as the action of verifying who an entity in the system is, and authorization refers to what actions and data they are allowed to perform and access. DERs, by their nature, introduce varied system ownership, operators, network interconnections, and control systems. This can create a larger attack surface for an adversary, necessitating strong authentication at every point.
"The grid is changing due to the many new devices and the push toward clean energy, and the new devices and communications systems are at a scale and complexity not previously used on the grid. These changes bring new cybersecurity challenges," White said. "With this clean energy transformation —and an exponential increase in the number of devices being introduced to the grid—we need to design security into the process early to guard against future threats."
This first cohort cycle for CECA aims to find solutions that can work within an OT environment with the accompanying communications protocols and system components and introduce innovative authentication practices where it does not currently exist. Accelerating the development and deployment of these solutions will help protect user access, facilitate system configuration changes, improve machine-to-machine communications, and authenticate commands, as well as provide a multitude of other options for increased authentication and authorization.
"This is exactly what the accelerator is about. We want to identify solutions that can help solve those problems and demonstrate the results so utilities can more confidently and rapidly adopt solutions that protect our grid," Macon said.
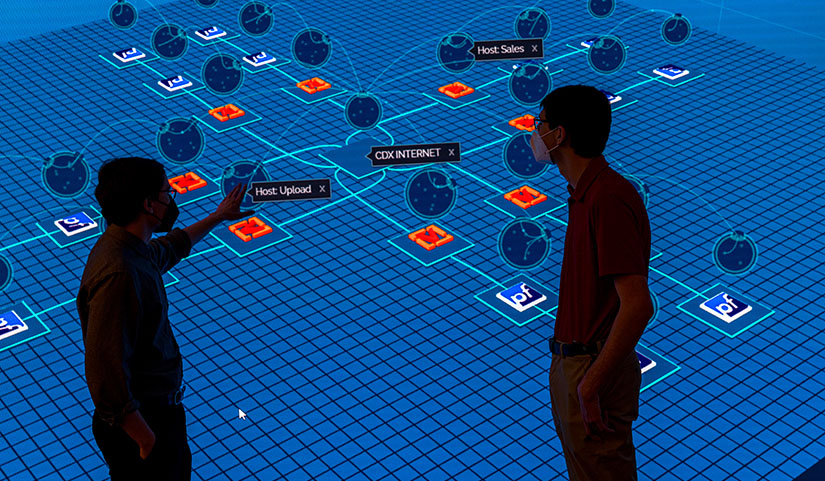
CECA cohorts go through a period to collaboratively validate solutions in the lab and demonstrate opportunity for real-world impact. To ensure participants are up to the cybersecurity standards necessary, NREL is using its Advance Research on Integrated Energy Systems (ARIES) cyber range. The cyber range allows users to evaluate technologies in a cyber-physical environment incorporating both virtual and physical assets, including power, control, and communications layers.
"The cyber range lets us build a representative environment of real-world networks. We can run through threat emulation scenarios or attacks without turning lights off in the real world," Macon said. "The ability to take potential solutions and see how they perform before implementation lowers the risk for our utility partners."
Solution providers will get the opportunity to demonstrate solutions to utilities, gain evaluation by NREL staff on solution performance, and receive a confidential technical assessment report demonstrating how the potential solution performed.
According to White, one of the most important parts of the program is bringing utilities together to discuss and agree on pathways to managing future cybersecurity risk, hopefully creating a template for the future.
"Involving the utilities and working together as a team is incredibly powerful," White said. "With NREL's fundamental mission to drive impact and change the grid, accelerators are a key pathway to achieve that goal. As this accelerator grows, brings in more partners, and connects with more solution providers, I think we will see the incredible impact."
For the CECA team, the program will be a true game-changer in securing the future grid.
"Cybersecurity threats to critical infrastructure continue to evolve quickly, and we need to stay on top of it even as we work toward a zero-emissions future," CECA Program Manager Ryan Brubaker said. "By offering world-class facilities, it allows cybersecurity innovators to change the game as they develop and deploy renewable, cost-effective, modern grid technologies along with a pathway to technical validation and demonstration."
Learn more about CECA and the application process.

